Apache and SSL
Updated on 23 Sep 2020
If you followed the previous tutorial you would’ve created a self signed SAN (Subject Alternative Name) certificate. In this tutorial we’ll learn how to set up Apache to use SSL.
Create the ssl params file
In /etc/apache2/conf-available directory, create a new file called ssl-params.conf. We use this file for our parameters instead of cluttering up our default-ssl.conf file which we modify in the next step.
SSLCipherSuite EECDH+AESGCM:EDH+AESGCM:AES256+EECDH:AES256+EDH
SSLProtocol All -SSLv2 -SSLv3 -TLSv1 -TLSv1.1
SSLHonorCipherOrder On
# Disable preloading HSTS for now. A real pain if you want to revert back to http later during testing.
# because the HSTS will force you back to https within the max-age limit...
# Header always set Strict-Transport-Security "max-age=63072000; includeSubDomains; preload"
Header always set X-Frame-Options DENY
Header always set X-Content-Type-Options nosniff
# Requires Apache >= 2.4
SSLCompression off
SSLUseStapling on
SSLStaplingCache "shmcb:logs/stapling-cache(150000)"
# Requires Apache >= 2.4.11
SSLSessionTickets Off
Modify default-ssl file
We need to modify the /etc/apache2/sites-available/default-ssl.conf file. There are 3 things we want to do
- Add the
servername(appears just under serveradmin) - change
SSLCertificateFileto our new certificate (from snakeoil) - change
SSLCertificateKeyFileto our new key (from snakeoil)
An abridged version of this file (with comments removed) is shown below
<IfModule mod_ssl.c>
<VirtualHost _default_:443>
ServerAdmin webmaster@localhost
ServerName localhost
DocumentRoot /var/www/html
#LogLevel info ssl:warn
ErrorLog ${APACHE_LOG_DIR}/error.log
CustomLog ${APACHE_LOG_DIR}/access.log combined
# SSL Engine Switch:
# Enable/Disable SSL for this virtual host.
SSLEngine on
SSLCertificateFile /etc/ssl/certs/apache-selfsigned.crt
SSLCertificateKeyFile /etc/ssl/private/apache-selfsigned.key
#SSLCertificateChainFile /etc/apache2/ssl.crt/server-ca.crt
<FilesMatch "\.(cgi|shtml|phtml|php)$">
SSLOptions +StdEnvVars
</FilesMatch>
<Directory /usr/lib/cgi-bin>
SSLOptions +StdEnvVars
</Directory>
</VirtualHost>
</IfModule>
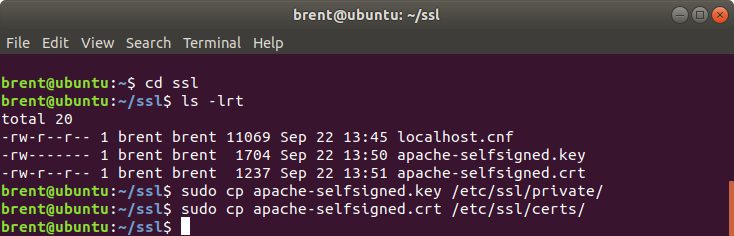
create the key and certificate
In the previous tutorial we learnt how to create a self-signed san certificate. Make sure the certificates we created are in the correct location and have the correct name we are refering to in /etc/apache2/sites-available/default-ssl.conf.
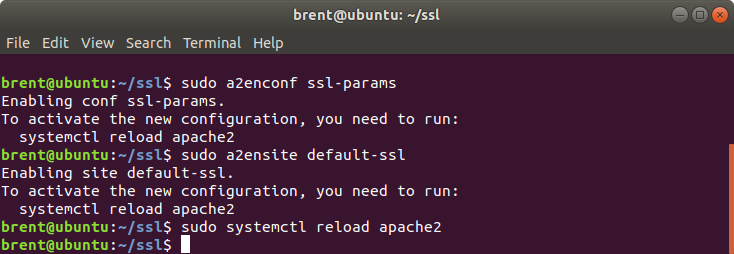
enable our changes
Now we need to enable our changes.
sudo a2enconf ssl-params
sudo a2ensite default-ssl
sudo systemctl reload apache2
test it out
Let’s see what happens when we try to go to localhost with https.
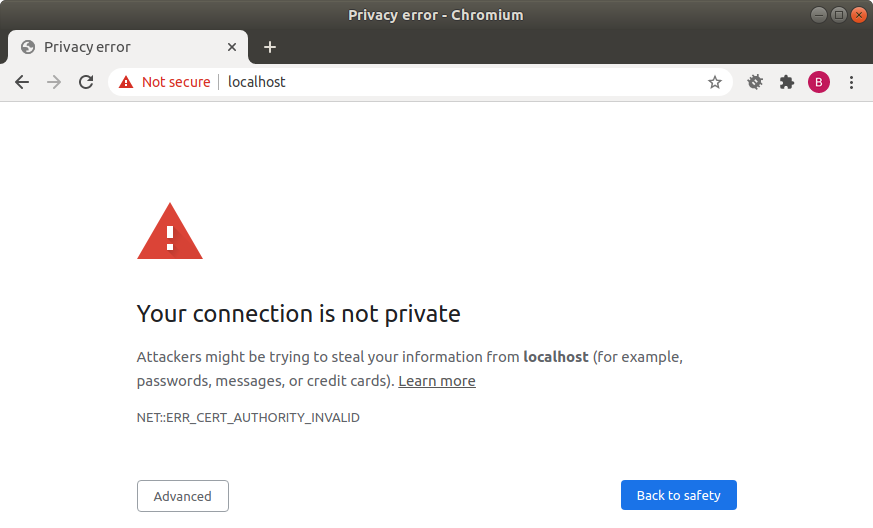
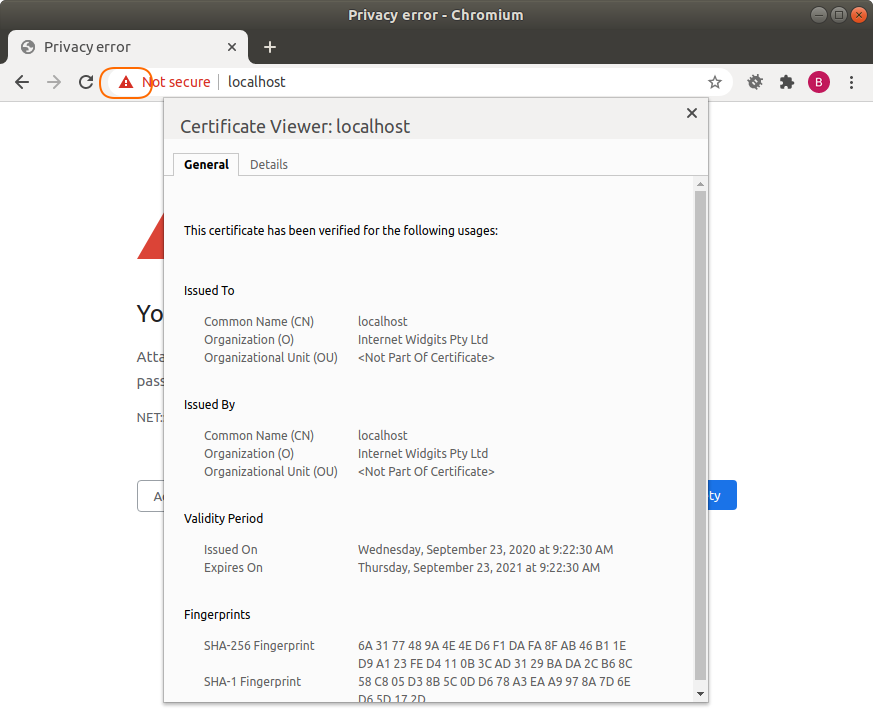
Not quite what we wanted. If we click on padlock icon (the part that says not secure in red in the address bar), we can see our SSL certificate we created, however the browser is rejecting it. The reason for the rejection is that it hasn’t been signed by a trusted certificate authority. In the next tutorial we’ll learn how to create a certificate authority, sign our certificate and load our https page without any errors.
being forced to https
If you’ve followed the steps so far and wish to go back to normal development, you might find you are being forced to use https. If this is the case in might be to do with HSTS (http strict transport security) and my other tutorial will show you how to deal with this issue.